If you’re holding cryptocurrency, the wallet you choose is the difference between sleeping soundly at night and checking your balance every hour in a cold sweat. I’ve seen investors lose tens of thousands of dollars not because of a market crash, but because they picked the wrong storage method. The wallet type you select fundamentally determines your exposure to hackers, platform failures, human error, and even your own forgetfulness. This isn’t a decision you can defer until “later” — it’s the foundation of your entire security strategy.
Understanding Crypto Wallets Before You Choose
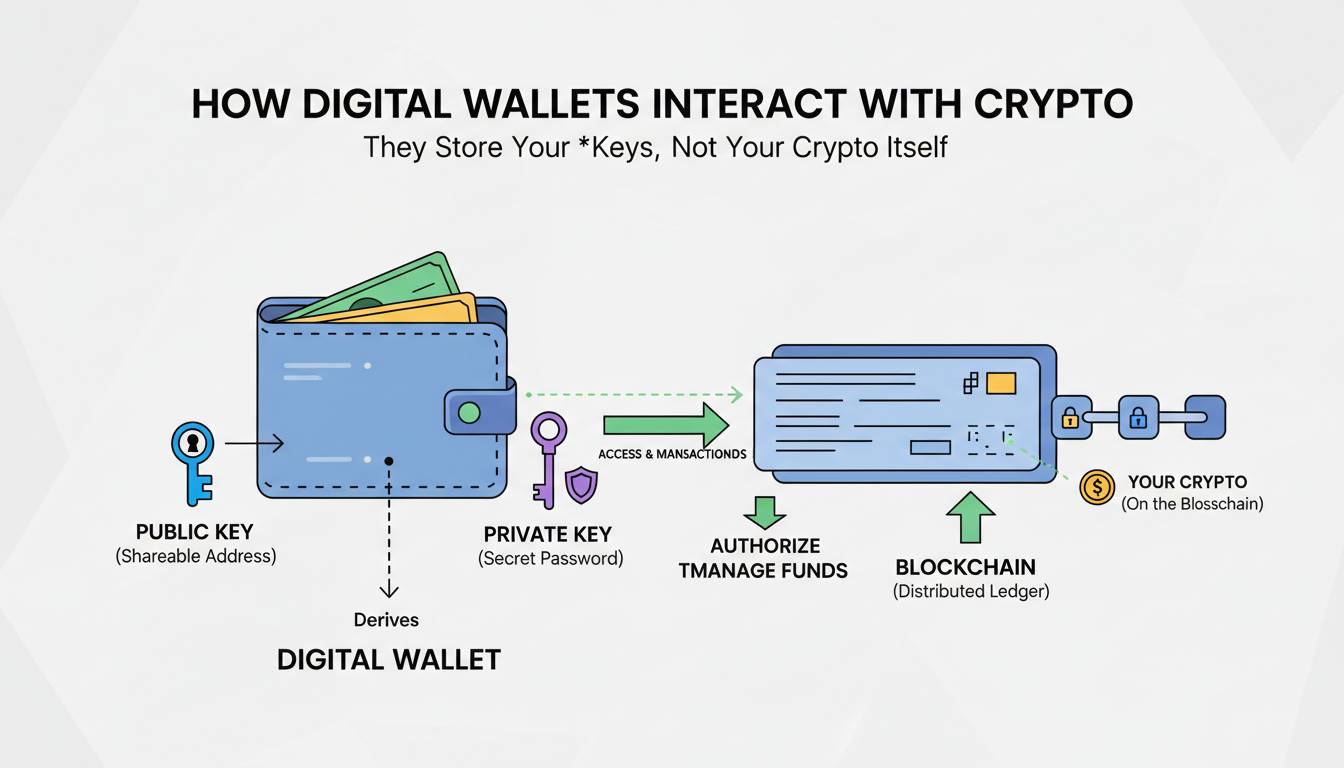
Before examining the four types, you need to understand what a crypto wallet actually does. Contrary to what the name suggests, a crypto wallet doesn’t store your coins directly. It stores your private keys — the cryptographic strings that prove you control your cryptocurrency and authorize transactions. Your coins exist on the blockchain; your wallet is the keyring.
Every wallet generates a public address (which you can share freely) and a private key (which should never leave your possession). When someone sends you Bitcoin, they’re directing it to your public address. When you want to spend it, your wallet uses your private key to sign the transaction. If someone obtains your private key, they have complete control over your funds — period. There’s no customer support number to call, no chargeback mechanism, no recourse.
This is why wallet selection isn’t about features or brand loyalty. It’s about understanding the trade-off between convenience and security, and matching that trade-off to your actual risk tolerance. Most people get this wrong because they think “security” means “strongest protection available.” It doesn’t. It means choosing the level of protection that matches how you actually live and work.
Hot Wallets: Convenience at a Price
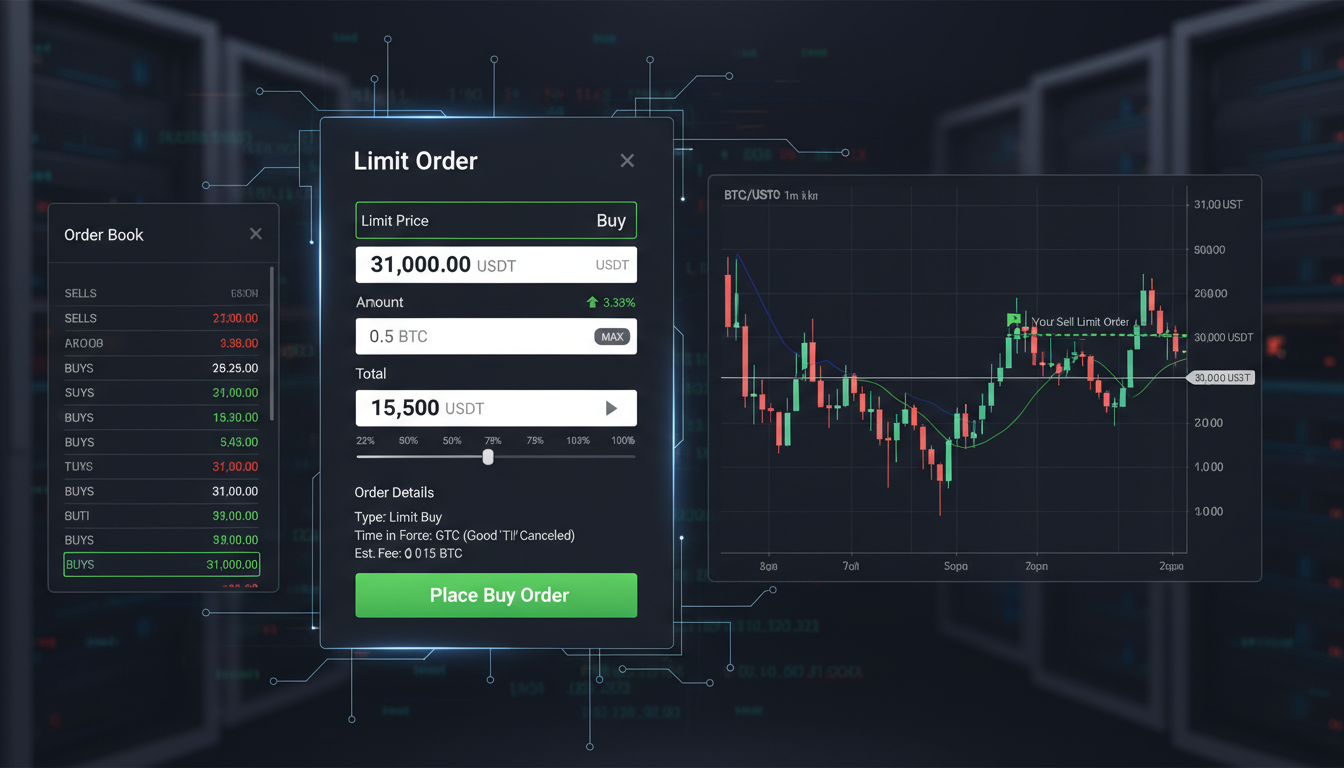
A hot wallet is any cryptocurrency wallet connected to the internet. This includes software wallets (desktop and mobile apps), web wallets (browser-based interfaces), and exchange wallets (where your crypto sits on a trading platform). The private keys exist somewhere online, whether on your device, a server, or an exchange’s infrastructure.
The most popular hot wallets include MetaMask (browser extension and mobile app), Coinbase Wallet (separate from your Coinbase exchange account), Trust Wallet (mobile-focused), and Exodus (desktop and mobile with built-in exchange features). These wallets have transformed from niche tools into mainstream products, with MetaMask alone reporting over 30 million monthly active users by late 2024.
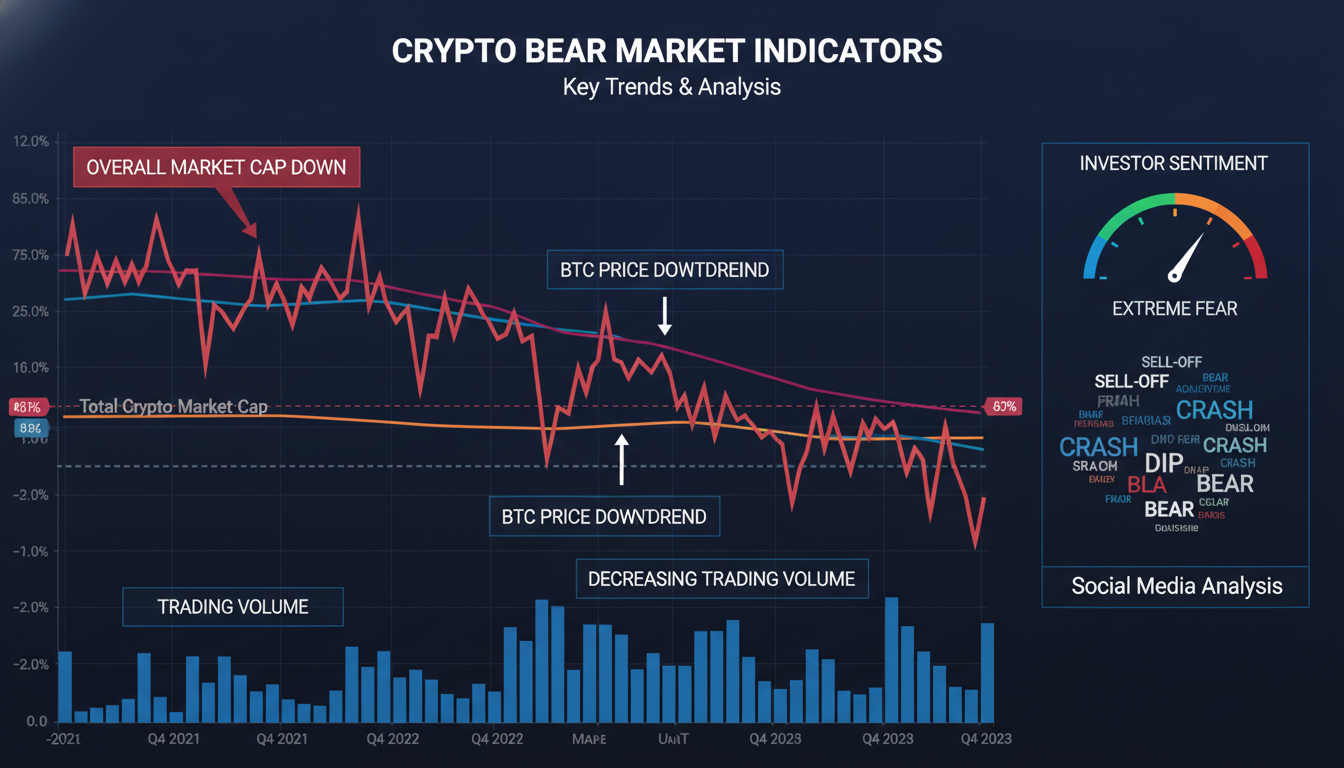
The risk is straightforward. Anything connected to the internet is potentially accessible to attackers. Hot wallets have been compromised through malware, phishing attacks, exchange hacks, and security vulnerabilities in the wallet software itself. The $610 million Poly Network hack in 2021 and numerous smaller exchange breaches demonstrate that even major platforms can fail. When you use a hot wallet, you’re trusting that the software developers, the platform operators, and your own device security will all hold up simultaneously.
Hot wallets excel at transaction speed and frequency. If you’re day trading, making regular purchases with crypto, or moving funds between exchanges frequently, a hot wallet reduces friction significantly. You can connect to decentralized applications (dApps), interact with DeFi protocols, and sign transactions in seconds rather than waiting for hardware device confirmation.
The real question isn’t whether hot wallets are safe — it’s whether the additional convenience justifies the increased risk for your specific situation. If you’re holding more than you can afford to lose entirely, hot storage alone is a gamble.
Cold Wallets: Offline Security for Serious Holdings
A cold wallet keeps your private keys completely offline, disconnected from the internet until you deliberately connect them to sign a transaction. The most common form is a hardware wallet — a physical device that generates and stores your keys in a secure element, never exposing them to your computer or phone.
Ledger and Trezor dominate this market. Ledger’s Nano X and Stax devices have sold millions of units, while Trezor’s Model T and Model One maintain a devoted following among privacy-conscious users. Cold wallets typically cost between $80 and $250, representing a significant upfront investment that signals you’re treating your crypto holdings seriously.
The security model is elegant in its simplicity. Your private keys never touch an internet-connected device during normal storage. When you want to send funds, you connect the hardware wallet, confirm the transaction on the device’s physical screen, and then disconnect. Even if your computer is riddled with malware, the attacker cannot access your keys because they’re physically unreachable.
This doesn’t mean cold wallets are invincible. They’ve been compromised through supply chain attacks (where devices are tampered with before reaching the user), firmware vulnerabilities, and operator error. In 2020, Ledger suffered a data breach exposing customer information, and researchers have demonstrated potential attack vectors on various hardware wallet models. The physical device can also be lost, damaged, or stolen — though most modern hardware wallets include PIN protection and recovery seed phrases that mitigate this.
Cold wallets suit anyone who holds significant cryptocurrency as a long-term investment. The convenience penalty is real: you can’t quickly move funds, interact with dApps, or check your portfolio from your phone without additional steps. But that friction is often the point. It forces intentionality into every transaction and dramatically reduces your attack surface.
Paper Wallets: The Bare Metal Approach
A paper wallet is exactly what it sounds like: your private keys and public addresses printed on paper. You generate them offline (ideally on a clean computer disconnected from the internet), print or write them down, and then never touch the digital version again. The keys exist only in physical form.
This was the original cold storage method, popularized in Bitcoin’s early years. When done correctly, it’s arguably the most secure form of cryptocurrency storage possible. There’s no software to hack, no device firmware to exploit, no online account to breach. The keys exist in the physical world, and unless someone literally steals the paper or photographs it before you secure it, they’re effectively unreachable.
The problems with paper wallets are practical rather than theoretical. Paper degrades — it gets wet, fades in sunlight, tears, and burns. People lose them. People accidentally throw them away. In the early Bitcoin era, countless stories emerged of people discarding paper wallets worth millions because they forgot where they’d hidden them or didn’t realize their significance. The Mt. Gox collapse also revealed that some early paper wallets had been generated on compromised computers, creating a false sense of security.
Modern cryptocurrency holders rarely use paper wallets as their primary storage method. The exception is for long-term “cold storage” of significant holdings where you want zero electronic attack surface. Some users create paper wallets as a backup to their hardware wallets, storing the paper in a safe deposit box or physical safe.
If you’re considering a paper wallet, be honest with yourself: do you have a system for securing physical documents that would survive a house fire, flooding, or decades of forgetfulness? Most people don’t. The security of a paper wallet is only as good as your physical security infrastructure.
Custodial Wallets: Someone Else Holds the Keys
When you keep crypto on an exchange like Coinbase, Binance, Kraken, or any trading platform, you’re using a custodial wallet. The exchange holds your private keys; you hold your account credentials. From your perspective, it feels like regular banking — you log in, see your balance, and initiate transfers through the platform’s interface.
The appeal is obvious: zero technical knowledge required, built-in customer support, easy access to trading features, and the ability to reset your password if you forget it. For beginners and casual users, custodial wallets remove nearly all the friction that makes self-custody intimidating.
The risk is equally obvious: you don’t control your keys, which means you don’t control your funds. When you deposit cryptocurrency on an exchange, you’re essentially making an unsecured loan to that platform. If the exchange gets hacked, goes bankrupt, freezes withdrawals, or faces regulatory action, you may lose access to your funds — with limited recourse. The collapses of FTX (2022), Celsius (2022), and Voyager (2022) demonstrated this risk in catastrophic fashion, leaving users billions of dollars short.
Even solvent and well-managed exchanges represent counterparty risk. They can freeze accounts, restrict withdrawals during high-volatility periods (as many did during the COVID-19 crash), or change their terms of service. Your legal claim to your cryptocurrency is only as strong as the exchange’s willingness to honor it and the legal jurisdiction’s ability to enforce that claim.
Custodial wallets make sense for active traders who need to move in and out of positions quickly, or for small amounts you intend to spend soon. They’re poor choices for long-term storage or significant holdings. The old advice — “not your keys, not your crypto” — remains sound, despite the convenience of custodial solutions.
Comparing the Four Types
| Factor | Hot Wallet | Cold Wallet (Hardware) | Paper Wallet | Custodial Wallet |
|---|---|---|---|---|
| Security Level | Low to Medium | High | High (if stored properly) | Low to Medium |
| Convenience | Very High | Medium | Low | Very High |
| Cost | Free to Low | $80–$250 | Minimal | Free (but platform fees apply) |
| Best For | Frequent trading, small amounts | Long-term holding, large amounts | Ultimate cold storage | Beginners, active traders |
| Key Risk | Online attacks, malware | Device loss/damage, supply chain | Physical loss, degradation | Exchange failure, hacking |
| Private Key Control | You | You | You | Third party |
The most common mistake I see is people using a hot wallet or exchange for their entire portfolio because it’s convenient, then being surprised when they read about the latest hack. Conversely, some people buy hardware wallets and never use them because the friction is too great, leaving their keys on a desk drawer where they provide neither security nor utility.
Matching Your Wallet to Your Risk Profile
Your risk profile isn’t just about how much money you can afford to lose. It’s about your technical competence, your time availability, your psychological tolerance for stress, and — critically — how you actually behave, not how you plan to behave.
The High-Risk-Tolerant Profile includes active traders, DeFi enthusiasts, and anyone who needs instant access to their funds for regular transactions. You probably use your crypto as a working asset rather than a store of value. A quality hot wallet like MetaMask or Coinbase Wallet serves you well, though you should still move significant holdings to cold storage when not actively trading. The key discipline: never keep more in hot wallets than you’d be comfortable losing in a single incident.
The Moderate-Risk Profile describes most serious investors. You hold cryptocurrency as part of a diversified portfolio, you’re not trading daily, but you want reasonable access in case of opportunities or emergencies. The hybrid approach works best here: maintain a hardware wallet for the majority of your holdings, with a small hot wallet balance for regular transactions and DeFi interaction. This gives you security for what matters while retaining convenience for what doesn’t.
The Security-First Profile applies if you’re holding life-changing money in cryptocurrency, you’re building long-term positions that won’t be touched for years, or you’re storing crypto for someone else (a child, a family member, an organization). Cold storage is non-negotiable. Consider multi-signature setups for added protection, where multiple keys are required to authorize transactions. Accept the inconvenience as the price of genuine peace of mind.
One counterintuitive truth most articles ignore: the safest wallet is the one you’ll actually use correctly. A hardware wallet locked in a drawer because it’s too inconvenient provides zero security. A hot wallet you’ve configured with two-factor authentication, hardware security keys, and a dedicated device might be safer than a cold wallet you never check or update. Security systems fail when they’re too burdensome for human beings to maintain.
Frequently Asked Questions
What is the safest type of crypto wallet?
Hardware cold wallets are generally considered the safest option for personal custody because the private keys never touch an internet-connected device. However, “safest” depends on your threat model — if you’re worried about physical theft, paper wallets or multi-signature setups might be more appropriate.
Are crypto wallets free?
Hot wallets and custodial wallets are typically free to download or use (though exchange wallets may charge trading fees). Hardware wallets cost between $80 and $250 as a one-time purchase. Paper wallets cost only the paper and ink, though the security burden is entirely on you.
What’s the difference between hot and cold wallets?
Hot wallets stay connected to the internet, offering convenience but exposing you to online attacks. Cold wallets remain offline until you deliberately connect them, maximizing security at the cost of convenience. This is the fundamental trade-off in cryptocurrency storage.
Can a hot wallet be secure?
Yes, but it requires discipline. Use hardware two-factor authentication (not SMS), keep your devices malware-free, enable all available security features, and never keep more than you’re willing to lose in a hot wallet. Many sophisticated users operate hot wallets safely by treating them as ephemeral — funds arrive, get used or moved, and the balance rarely sits for long.
What happens if I lose my hardware wallet?
Nothing, as long as you have your recovery seed phrase (the 12–24 words generated when you set up the wallet). You can purchase a new hardware wallet or use compatible software to restore access to your funds using that seed phrase. This is why the seed phrase must be stored securely and privately — anyone with access to it can control your funds.
The Honest Reality
Here’s what most crypto wallet guides won’t tell you: no solution is permanent, and no choice is final. The cryptocurrency storage landscape continues to evolve. New wallet technologies emerge. Regulatory changes may affect custodial options. Your own needs will shift as your portfolio grows and the market matures.
The best wallet for you today might not be the best wallet for you in three years. Review your setup periodically. Test your recovery procedures before you need them. Accept that security is an ongoing practice, not a one-time decision.
What matters most isn’t picking the theoretically perfect wallet — it’s understanding why you made that choice and maintaining the habits that make it work. Your cryptocurrency is only as secure as your willingness to treat it that way.