The average crypto holder loses more than $3.5 billion annually to wallet hacks, and the number is climbing. What’s worse: the majority of these thefts are preventable. I’ve spent years tracking wallet security incidents for crypto platforms, and I can tell you that most people assume their funds are safe because they use a reputable exchange or a hardware wallet. That assumption is exactly what hackers count on.
This guide breaks down the actual attack methods criminals use to drain wallets, the warning signs most people miss, and the concrete steps you can take right now to protect your holdings. I’m not going to cover theoretical vulnerabilities or scenarios that only exist in lab environments. Every technique here has been used in real thefts within the past two years.
Phishing Attacks: The Most Common Entry Point
Phishing remains the dominant attack vector, responsible for roughly 70% of individual wallet compromises. The math is simple: it’s easier to trick a person than to break encryption.
The classic approach involves fake websites that mirror legitimate exchanges or wallet interfaces. In early 2024, attackers launched convincing copies of popular DeFi protocols, capturing login credentials and private keys from users who thought they were connecting their wallets to legitimate dApps. The URL differences were subtle—a swapped letter, a different domain extension—and the interfaces were pixel-perfect replicas.
But the more sophisticated variant targets you directly through your browsing session. Attackers inject malicious code into legitimate websites through third-party scripts or compromised advertising networks. When you visit a crypto forum or even a news site, the script detects your IP address and location, then serves a customized popup asking you to reconnect your wallet. The call-to-action feels authentic because the attacker knows you’re already in a crypto mindset.
The most recent evolution involves DNS hijacking. Attackers compromise domain name registrars to redirect traffic from legitimate crypto sites to phishing pages. In March 2024, the domain registrar Squarespace experienced a breach that affected multiple crypto companies, redirecting users to malicious sites for hours before the issue was discovered.
The takeaway here is straightforward: never click links in emails, direct messages, or social media posts claiming to be from your wallet provider. Navigate to exchanges and wallet sites by typing the URL directly into your browser. Enable the U2F (Universal 2nd Factor) authentication standard on every account that supports it. This is distinct from SMS-based 2FA, which has its own vulnerabilities.
Malware and Keyloggers: The Threat Inside Your Device
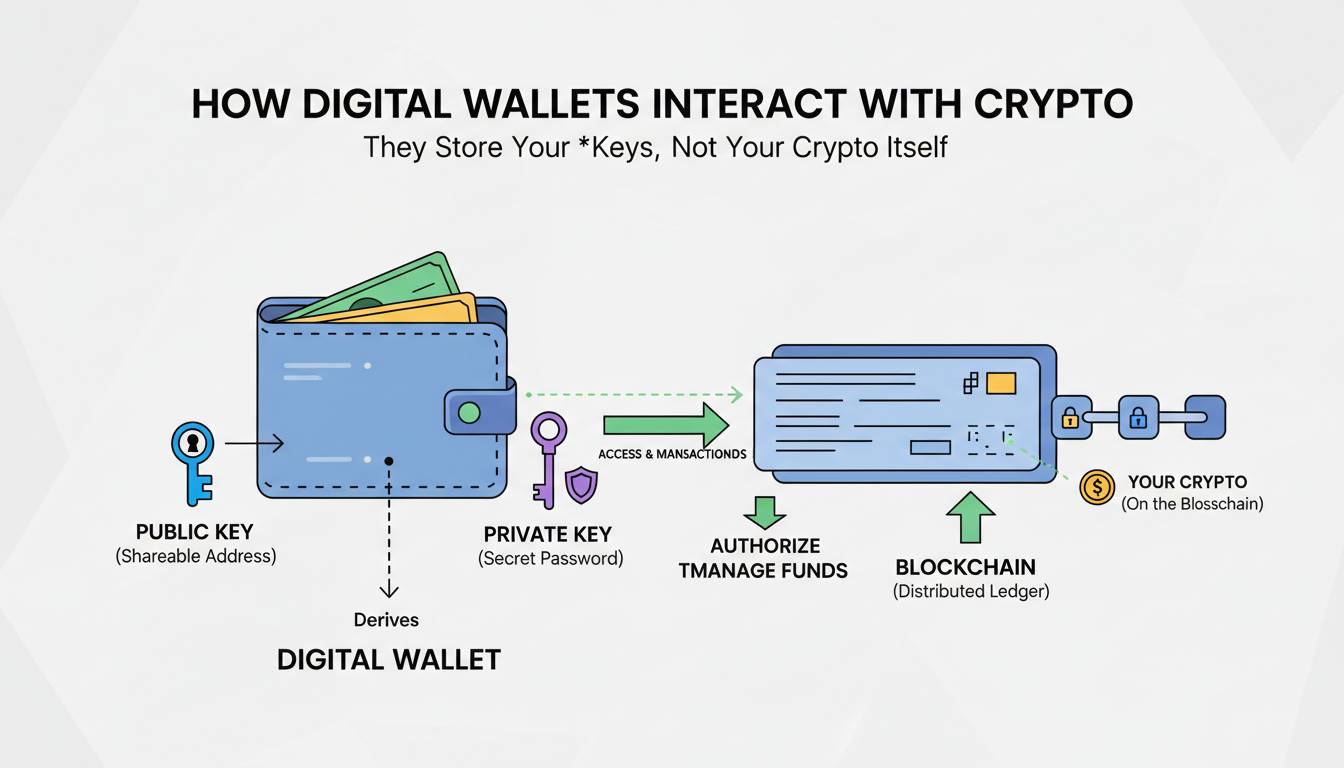
Malware specifically designed to target cryptocurrency wallets has become a cottage industry. These programs don’t try to breach your wallet’s encryption directly. Instead, they wait for you to enter credentials or copy a wallet address, then they intercept and replace that data before it reaches the legitimate destination.
Clipboard hijackers represent the simplest version. When you copy a receiving address to send funds, the malware silently replaces it with an address controlled by the attacker. You paste what looks like your intended address, confirm the transaction, and your funds vanish into a wallet you don’t control. This type of malware has been found in pirated software, browser extensions, and even legitimate-looking mobile apps submitted to app stores under false pretenses.
More aggressive malware goes after your entire device. Remote access trojans (RATs) can capture screenshots, record keystrokes, and in some cases, inject fake transaction confirmations that trick you into sending funds to compromised addresses. In late 2024, security researchers at Sophos identified a new strain of information-stealing malware that specifically targeted browser-based cryptocurrency wallets, exfiltrating seed phrases stored in browser extensions before the user even initiated a transaction.
The uncomfortable truth is that mobile devices are particularly vulnerable. Android’s permission system allows malware to overlay fake interfaces on top of legitimate wallet apps—a technique called “overlay attacks.” When you open your wallet app, the malware displays a convincing replica asking you to re-enter your seed phrase for “security verification.” By the time you realize what happened, your wallet is drained.
Practical defense requires layering: keep your operating system and security software updated, never download apps outside official stores, and most importantly, verify every transaction address on a separate device or through a hardware wallet before confirming. If you’re transacting significant amounts, assume your everyday device may be compromised and use an isolated, security-focused system for crypto operations.
Exchange Platform Breaches: When the Custodian Fails
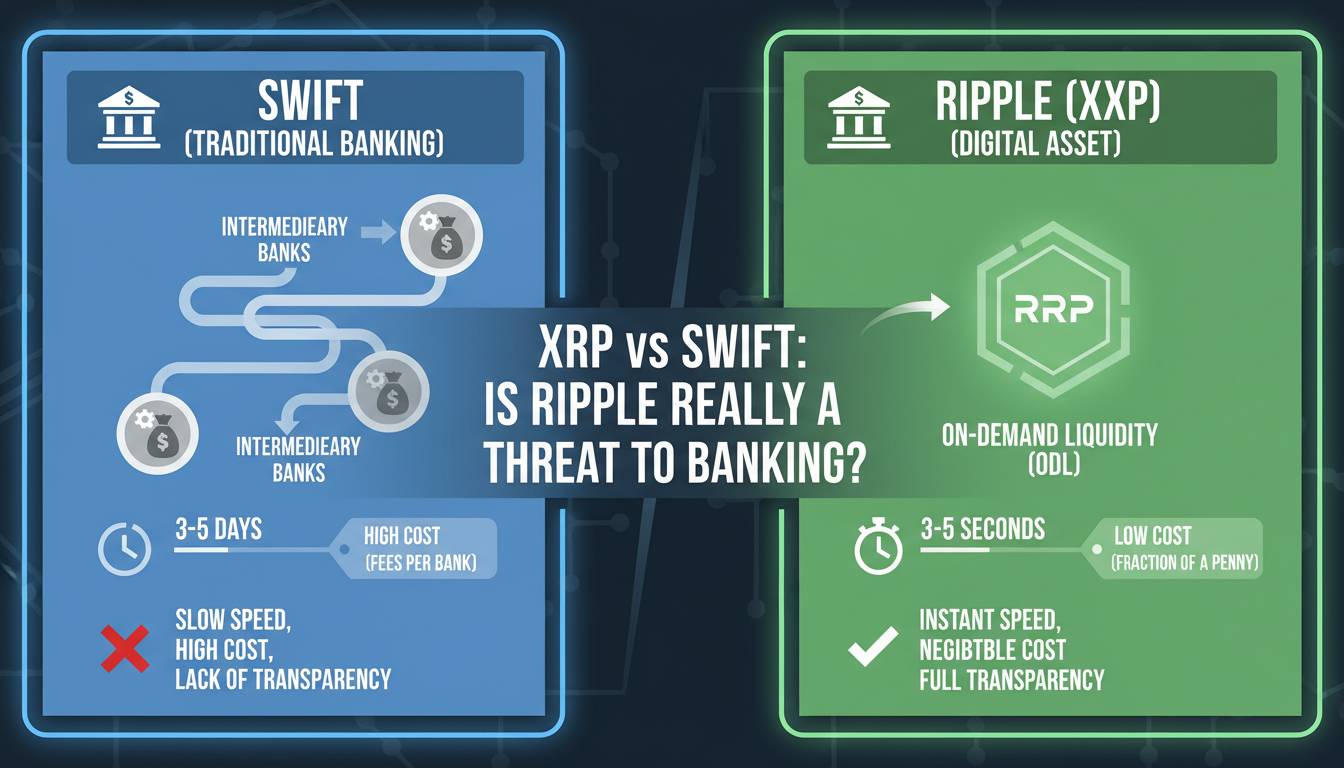
When you hold funds on an exchange, you’re trusting that platform’s security infrastructure. That trust has been violated repeatedly. The difference between self-custody and exchange custody is the difference between holding your own cash and leaving it in a bank’s vault—but exchanges have proven far more vulnerable than traditional banks.
The 2022 collapse of FTX is the most famous example, but it’s not purely a security breach. It involved institutional fraud. More instructive are actual hack incidents. In July 2024, the Indian exchange WazirX suffered a breach that resulted in approximately $230 million in losses. Attackers exploited vulnerabilities in the platform’s multi-signature wallet infrastructure, compromising enough private keys to authorize unauthorized transfers.
The root cause in most exchange breaches isn’t sophisticated zero-day exploits. It’s configuration errors and inadequate access controls. Internal systems get misconfigured, hot wallets get connected to the internet when they shouldn’t be, and private keys get stored in systems that attackers can reach through phishing or credential stuffing.
What this means for you is uncomfortable: even the most reputable exchanges have been breached. Coinbase, Binance, and Kraken have all experienced security incidents over the years, though they’ve generally maintained sufficient reserves to cover customer losses. The smaller or newer the exchange, the higher your risk.
The straightforward advice is to limit what you hold on exchanges to what you’re actively trading. The rest should go to self-custody solutions that you control. This isn’t about distrusting exchanges. It’s about acknowledging that your security is only as strong as the platform’s weakest link, and you have no visibility into that infrastructure.
SIM Swapping: Hijacking Your Phone Number
SIM swapping exploits a fundamental weakness in cellular network authentication. Attackers contact your mobile carrier, convincingly impersonate you, and convince customer service to transfer your phone number to a SIM card they control. Once they have your number, they can receive SMS-based verification codes and bypass two-factor authentication on your accounts.
The reality is that SIM swapping is easier than most people assume. Social media presence makes it trivial for attackers to gather the personal information needed to convince carrier representatives they’re you. In 2023, a cryptocurrency investor successfully sued AT&T for $1.8 million after attackers used SIM swapping to steal millions in crypto. The carrier’s inadequate verification procedures enabled the theft.
What makes this attack particularly dangerous is that it bypasses every password and security question you’ve set up. Your email, your exchange accounts, your wallet recovery options—many of them fall back to SMS verification. Once the attacker controls your phone number, they can trigger password resets, intercept codes, and drain accounts before you realize anything is wrong.
Defense requires separating your phone number from your security infrastructure. If your crypto accounts support it, remove your phone number as a recovery option entirely. If that’s not possible, set up a dedicated phone number used only for crypto accounts, kept separate from your personal number. This makes social engineering against carrier employees much harder because there’s less public information linking that number to your crypto holdings.
Social Engineering: The Human Vulnerability
Every technical security measure has a human operating it, and skilled attackers target the operator rather than the system. Social engineering in crypto takes many forms, but they all share a common goal: manipulating you into voluntarily transferring funds or revealing credentials.
The “customer support” scam is perennial. Attackers create fake support accounts on Twitter, Discord, or Telegram, then reach out to users who have posted questions about problems with their wallets. The fake support agent offers to help, asks for your account details “to verify your identity,” and uses that information to drain your wallet. In early 2025, scammers impersonating MetaMask support successfully stole over $500,000 from users in a single campaign.
More sophisticated social engineering involves building trust over time. Attackers join crypto communities, participate in discussions, and establish reputations as helpful community members. Months later, when they’ve earned trust, they share a “sure thing” investment opportunity or a “bug bounty” that requires connecting a wallet to a malicious dApp. The target, already comfortable with the person, doesn’t scrutinize the transaction.
The defense isn’t technical—it’s psychological. No legitimate support agent will ever ask for your seed phrase, private keys, or password. No investment opportunity requires you to connect your wallet to a site you haven’t thoroughly vetted. No customer support ticket gets resolved by you providing credentials. When someone contacts you with an offer or request related to crypto, assume it’s a scam until you’ve verified their identity through channels you initiated.
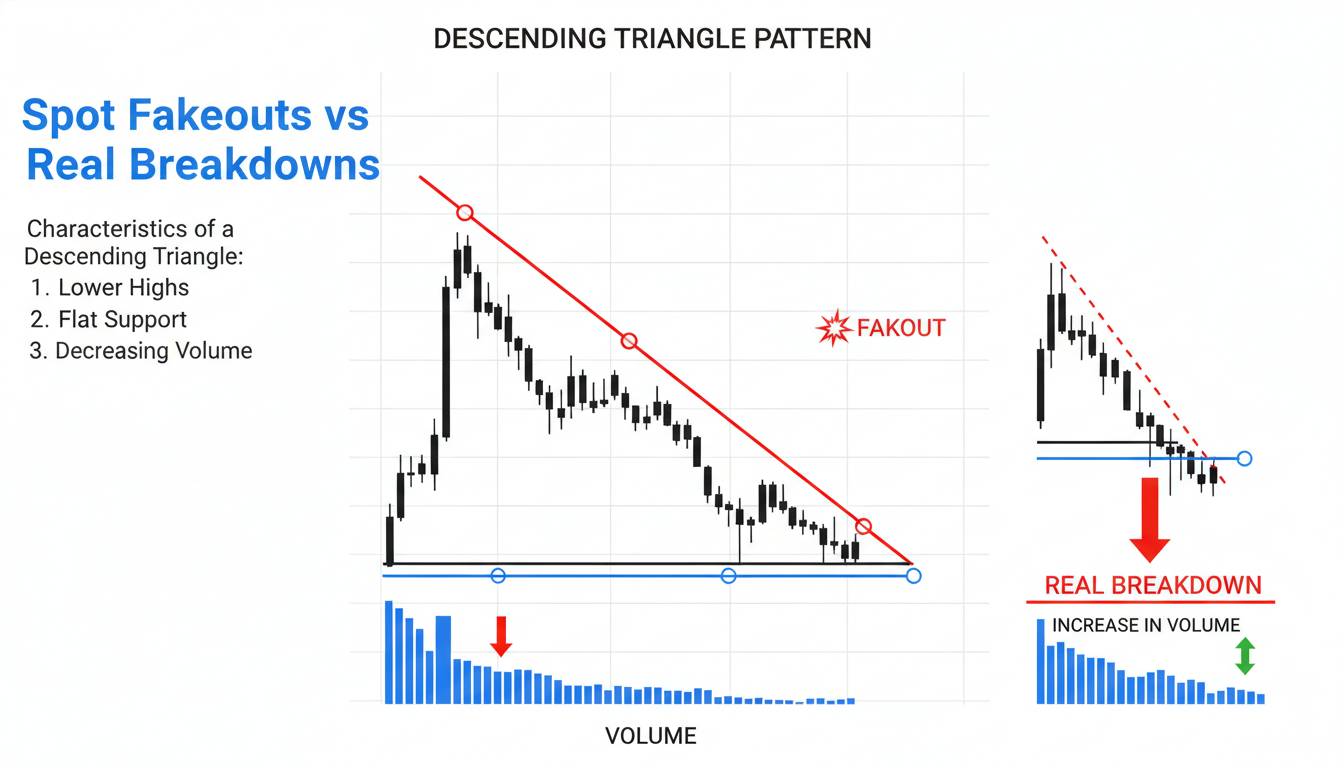
Smart Contract Exploits: When Code Becomes the Attack Surface
Not all wallet compromises start with user error. Smart contracts—the self-executing programs that power DeFi protocols—have vulnerabilities that can drain funds from wallets connected to them. When you interact with a DeFi protocol, you’re granting it some level of access to your wallet. If that protocol has a flaw, attackers can exploit it to withdraw more than you intended.
The most common exploit involves approval manipulation. When you use a DeFi application, it requests permission to spend a certain amount of your tokens. Malicious contracts can request unlimited approvals, then drain your entire balance once you’ve connected your wallet. In 2024 alone, approval scams resulted in losses exceeding $300 million across the DeFi ecosystem.
Flash loan attacks represent another vector. Attackers borrow massive amounts of cryptocurrency without collateral, manipulate token prices on decentralized exchanges, execute arbitrage, and repay the loan—all within a single blockchain transaction. While the technical vulnerability lies in the protocol’s price oracle implementation, the result is that users who provided liquidity to affected pools lost their funds.
The uncomfortable reality is that you cannot fully audit smart contract security yourself unless you’re an experienced blockchain developer. Even professional audits miss vulnerabilities. In August 2024, the decentralized exchange Curve Finance suffered an exploit that stole approximately $70 million, despite the protocol having undergone multiple security audits.
When using DeFi protocols, limit your exposure to amounts you’re willing to lose. Review the permissions you’ve granted using tools like Etherscan’s token approval checker, and revoke unnecessary approvals after completing your transactions. Don’t connect your primary wallet to new or experimental protocols—use a separate wallet with limited funds specifically for DeFi interactions.
Warning Signs Your Wallet May Be Compromised
Identifying a compromise early can mean the difference between losing your funds and recovering them. The signs aren’t always obvious, but they’re there if you know what to look for.
Unexpected transactions are the most obvious indicator. Check your wallet’s transaction history regularly—even small, test transactions can signal that someone has access. Attackers sometimes make small transfers to verify the wallet is active before draining it.
Login alerts from exchanges or wallet providers about new device access deserve immediate attention. If you didn’t log in from a new location or device, treat it as a potential compromise and change your credentials immediately.
Device performance issues can indicate malware. Unexpected slowdowns, unfamiliar processes running in the background, or browser extensions you didn’t install are all red flags. Mobile users should watch for battery drain, unusual data usage, or apps requesting permissions they shouldn’t need.
What To Do If Your Wallet Is Hacked
If you discover unauthorized transactions or suspect your wallet is compromised, act immediately.
First, disconnect the wallet from any connected dApps or websites. If you’re using browser-based wallets like MetaMask, revoke token approvals using a revocation tool like revoke.cash. This prevents attackers from draining any remaining balance.
Second, move remaining funds to a new wallet with a fresh seed phrase. Do not attempt to recover or clean your existing wallet—assume it’s compromised and start fresh.
Third, report the incident to the exchange or platform involved. While recovery is rare, reporting creates a record that can aid in investigations and potentially freeze stolen funds if they reach a centralized exchange.
Finally, document everything. Transaction hashes, timestamps, communications with attackers if any occurred, and screenshots of your wallet interface. This information can be valuable for forensic analysis or legal proceedings.
Frequently Asked Questions
Can someone hack my MetaMask wallet? Yes. MetaMask has been targeted by phishing campaigns, malware, and fake browser extensions. The wallet itself has strong security architecture, but user behavior determines its actual safety.
What is the safest crypto wallet? Hardware wallets from reputable manufacturers like Ledger and Trezor provide the strongest security for most users. They store private keys in isolated secure elements that never expose the keys to connected devices.
Can a crypto wallet be hacked even with 2FA? Yes. SMS-based 2FA can be bypassed through SIM swapping. Hardware-based 2FA or U2F tokens provide significantly stronger protection.
How do I know if my crypto wallet is compromised? Monitor for unrecognized transactions, unexpected login alerts, and unusual device behavior. Regularly review your transaction history and connected applications.
Conclusion
The threat landscape for cryptocurrency wallets is not theoretical—it’s active, evolving, and responsible for billions in losses annually. But here’s what the security industry won’t tell you in most articles: the solutions aren’t complicated. They’re just not convenient.
Use hardware wallets for significant holdings. Verify every transaction address. Keep your seed phrase offline and private. Limit exchange balances to what you’re actively trading. Assume every link, every DM, and every “support” contact is potentially hostile.
The cat-and-mouse game between attackers and defenders continues, and attackers are inventive. But most thefts succeed not because of sophisticated exploits but because of basic security failures. Your goal isn’t to be impenetrable—it’s to be harder to compromise than the next person. That’s usually enough.
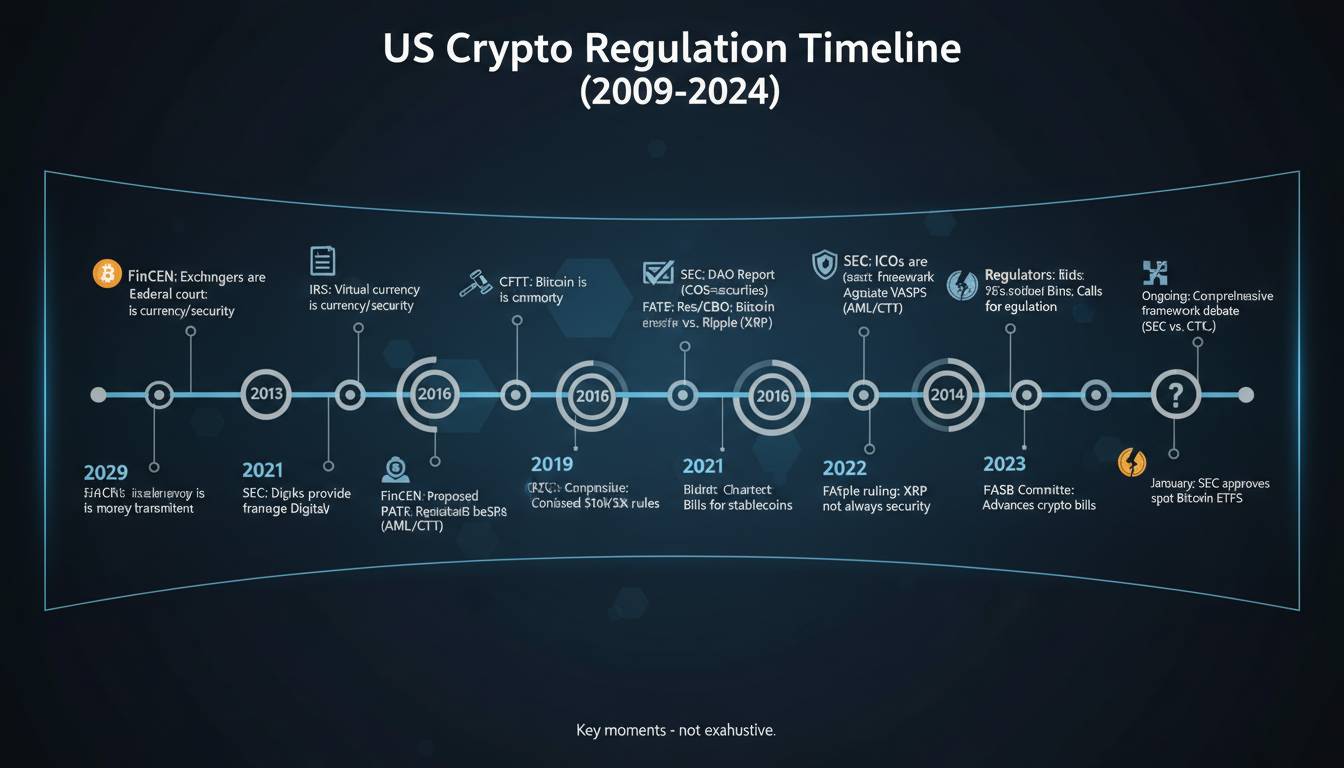
What remains unresolved is whether the industry will ever provide better consumer protections or whether the burden will continue to fall entirely on individual users. Regulatory clarity is coming, but slowly. In the meantime, your crypto security is ultimately your responsibility—and that responsibility begins with understanding what you’re defending against.