If you’ve ever sent Bitcoin to a friend or withdrawn Ethereum to a hardware wallet, you’ve participated in one of the strangest concepts in modern technology: your digital wallet never actually holds your cryptocurrency. It holds something far more valuable—and far easier to lose. Understanding this distinction isn’t just technical trivia; it’s the difference between safely managing your crypto and one day discovering your funds have vanished into the blockchain forever.
This article goes beneath the surface of what “wallet” means in cryptocurrency contexts. You’ll learn exactly what your wallet stores, why the distinction matters for security, and how to choose the right storage approach for your situation. I also challenge some conventional wisdom about what makes a wallet “safe” that you’ll hear repeated in crypto circles.
The Core Paradox: Your Crypto Lives on the Blockchain
When you own cryptocurrency, where is it actually located? The answer is: everywhere and nowhere. Your Bitcoin, Ethereum, or Solana doesn’t sit in a file on your computer or in a server at some crypto company. It exists as a record on the blockchain—a distributed ledger maintained by thousands of nodes worldwide.
What you own is the ability to transfer those tokens. That ability is controlled by your private key, a cryptographic string of numbers that functions like the combination to a safe. The blockchain records that “address X owns Y amount of token Z,” but only the holder of the corresponding private key can authorize a transfer from that address to another.
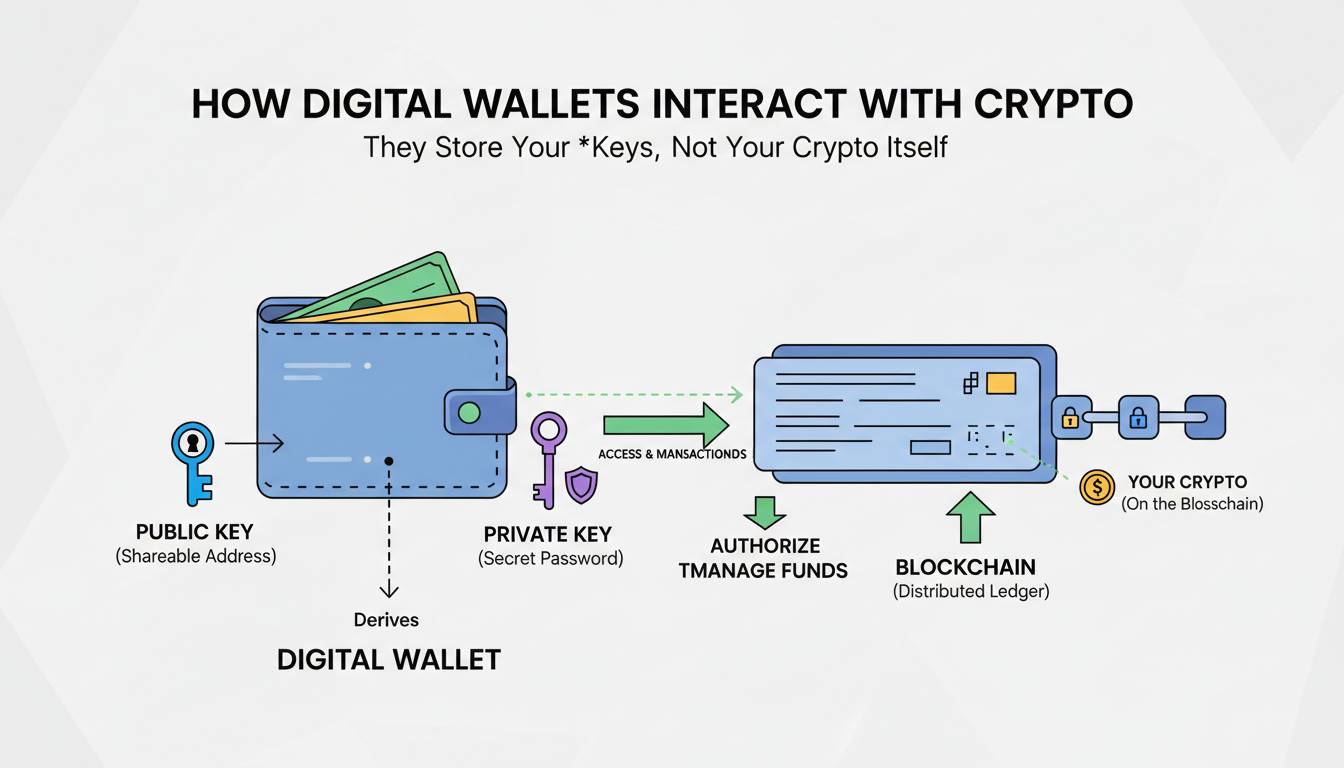
This is the key insight that most introductory crypto articles don’t communicate clearly: your digital wallet is not a container. It’s a keyring. It holds the keys that let you access your funds, not the funds themselves. Coinbase, MetaMask, Ledger, Trust Wallet—none of them actually hold your crypto. They hold the credentials that prove you control your crypto.
This distinction matters enormously when you consider what happens if you lose your phone, forget your password, or the wallet company goes out of business. Your crypto remains on the blockchain exactly where it always was. As long as you have your private key or seed phrase, you can import your wallet into any compatible software and access your funds immediately. But if you lose your keys and have no backup, your crypto becomes inaccessible forever—not because it disappeared, but because you’ve lost the only proof that it’s yours.
What Your Wallet Actually Contains
Now that you understand the conceptual framework, let’s get specific about what your crypto wallet actually stores on your device. Every functional wallet maintains three interrelated pieces of cryptographic data.
Your private key is the master secret—a 256-bit number (often displayed as a 64-character hexadecimal string) that gives complete control over your crypto. If someone obtains your private key, they can transfer all your funds to their address with no recourse. This is why private keys must remain absolutely secret. In modern wallets, your private key is typically derived from a seed phrase—a series of 12 or 24 words generated using the BIP39 standard—which serves as a human-readable backup of your entire wallet.
Your public key is mathematically derived from your private key through elliptic curve cryptography. The relationship is one-way: anyone can calculate a public key from a private key, but reversing that process is computationally infeasible. Your public key functions like an account number that you can safely share with others so they can send you crypto.
Finally, your wallet address is a shortened hash of your public key, typically 26-35 characters beginning with various prefixes depending on the cryptocurrency (1 for Bitcoin legacy addresses, 0x for Ethereum). This is what you share with others to receive funds. The address is public information—anyone can send crypto to it—but only the holder of the corresponding private key can authorize withdrawals.
When you set up a new wallet in MetaMask, Trust Wallet, or any other software, the application generates these cryptographic credentials locally on your device. The private key is then encrypted and stored in the wallet’s local storage, protected by your password or biometric authentication. Nothing is sent to any server, unless you’re using a custodial wallet, which operates on an entirely different model.
This is also why seed phrase backups are so critical. If your device fails, is lost, or is stolen, you can reinstall the wallet application on new hardware and enter your seed phrase to regenerate your private key and restore access to all your addresses. The crypto never left the blockchain; you simply needed your key to prove ownership again.
How Transactions Actually Move Crypto
Understanding what wallets store gets you halfway there. The other half is understanding what happens when you actually use your crypto, which is to say, when you sign and broadcast a transaction.
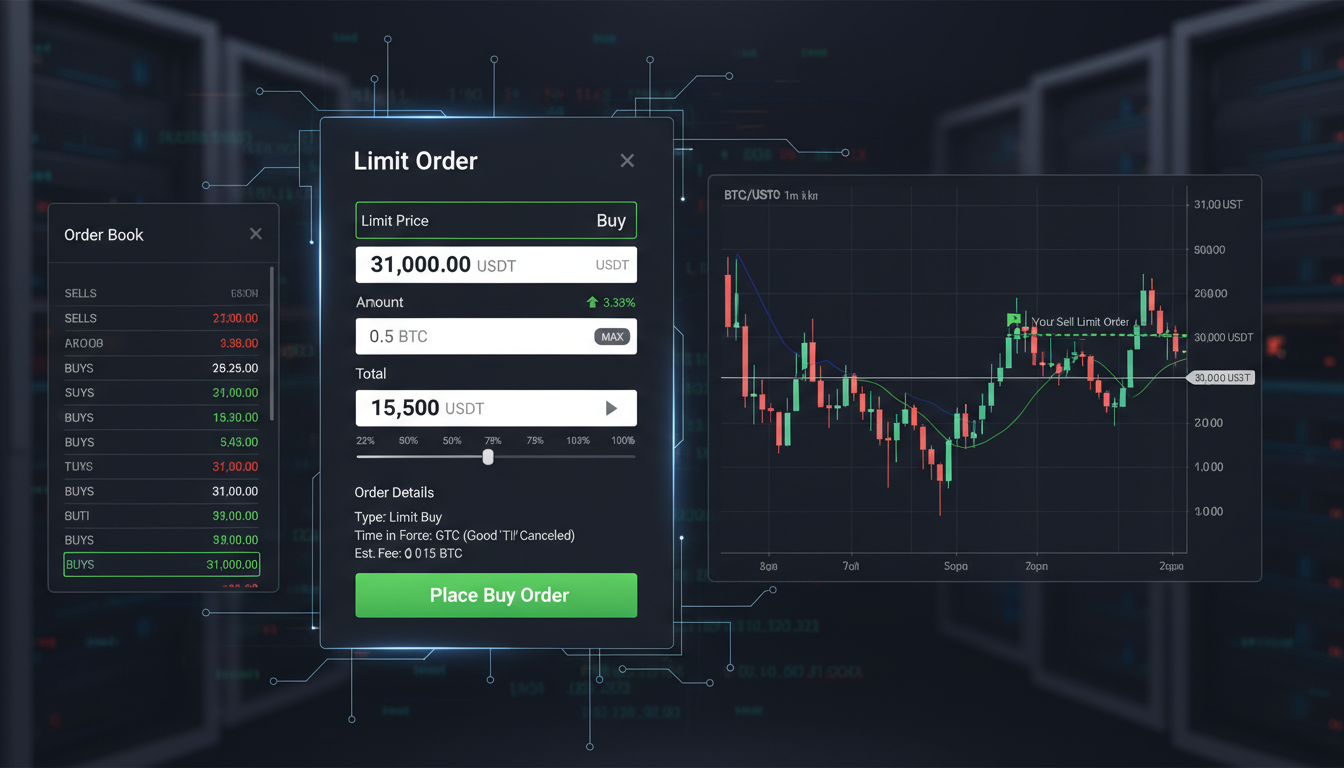
Let’s walk through the complete process. When you decide to send 0.1 Bitcoin to a friend, your wallet constructs a transaction message specifying the recipient’s address, the amount, and a transaction fee. This message is essentially data—it hasn’t been submitted anywhere yet.
Your private key becomes essential here. Your wallet uses your private key to create a digital signature that proves you authorized this specific transaction. The signature is mathematically linked to both your private key and the transaction data itself, meaning three things are true: the signature is mathematically impossible to forge, the signature proves you had access to the private key without revealing the key itself, and the signature would be invalid if even a single character of the transaction data were altered.
Once signed, your wallet broadcasts the transaction to the cryptocurrency network. Nodes across the network receive your transaction and verify the signature using your public key. If the math checks out—if your address contains sufficient funds, if the signature is valid, if all the technical rules are satisfied—the transaction enters the mempool, a waiting area for unconfirmed transactions.
From there, miners or validators (depending on the blockchain) group your transaction into a block and add it to the blockchain. Once confirmed, the ledger permanently records that your address now holds 0.1 Bitcoin less than before and the recipient’s address holds 0.1 Bitcoin more. No crypto physically moved through any wire or server. The blockchain simply updated its records, and your private key was the cryptographic proof that you had the authority to request that update.
This is why security experts emphasize private key protection so intensely. The blockchain itself is virtually unhackable, compromising it would require controlling a majority of network nodes. But stealing someone’s private key gives you the ability to sign a valid transaction transferring all their funds to your own address, and the blockchain will honor that signature without any way to reverse it.
Hot Wallets vs Cold Wallets: The Security Trade-off
One of the most important distinctions in crypto storage is between hot wallets and cold wallets, and this is where I want to push back against some conventional wisdom you’ll encounter.
A hot wallet is any wallet whose private keys are stored on an internet-connected device. MetaMask in your browser, the mobile app for Trust Wallet, your Coinbase exchange account, these are all hot wallets. They’re called “hot” because they’re online, which means they’re potentially accessible to hackers, malware, or phishing attacks.
A cold wallet keeps your private keys completely offline. The most common form is a hardware wallet, a physical device like those made by Ledger or Trezor that generates and stores your private keys on isolated firmware, never exposing them to your computer or phone. When you want to sign a transaction, the transaction data is sent to the hardware wallet, the wallet signs it internally using your private key (which never leaves the device), and then the signed transaction is broadcast to the network. Your private key was never on an internet-connected machine.
Now here’s where conventional wisdom gets it wrong: the assumption that cold wallets are inherently “safer” than hot wallets for everyone. This is technically true in terms of attack surface, but practically speaking, cold wallets introduce a different set of risks that often get ignored in the crypto purist advice to “always use a hardware wallet.”
If you store your life savings on a Ledger device and then lose that device with no seed phrase backup, your money is gone just as surely as if you’d lost your private key on a hot wallet. If your hardware wallet is destroyed in a house fire and you didn’t store your seed phrase in a separate location, you’re in the same situation. Hardware wallets also introduce a supply chain risk, it’s theoretically possible for a sophisticated attacker to intercept a device in shipping and modify its firmware to exfiltrate your seed phrase when you eventually use it.
The real security calculus isn’t hot vs cold. It’s about threat modeling: what risks are you actually facing? If you’re holding a few hundred dollars of crypto on a mobile wallet and practicing basic opsec, strong unique passwords, two-factor authentication, avoiding suspicious links, you’re probably fine. If you’re holding your life savings in crypto, the additional friction and complexity of a hardware wallet probably makes sense. But the blanket advice that “you should only use cold storage” ignores the fact that many people actually introduce more risk when they adopt complex security practices they don’t fully understand.
The best security is the security you’ll actually use consistently.
The Four Main Types of Crypto Wallets
Given this foundation, let’s examine the major categories of wallets available and when each makes sense.
Software wallets are applications that run on your computer, phone, or browser. MetaMask is the dominant Ethereum and EVM-compatible wallet, used by millions for DeFi, NFTs, and general token management. Exodus, Atomic Wallet, and Trust Wallet fall into this category. Software wallets are convenient, they let you interact with decentralized applications seamlessly, but your private keys live on an internet-connected device with all the attendant risks. Most software wallets give you full control of your keys (non-custodial), but some, like the wallet built into Binance or Coinbase, may hold keys on your behalf (custodial).
Hardware wallets are dedicated physical devices that store your private keys in secure elements. Ledger and Trezor are the most established brands. These devices cost between $80 and $250, but they provide the strongest practical protection against remote attacks. The private key is generated in an isolated environment and never leaves the device. Your computer or phone sees only the signed transaction output. For anyone holding significant crypto amounts, hardware wallets represent the current standard for personal security. But remember: the seed phrase printed on the paper card in your drawer is what actually protects you, not the device itself.
Paper wallets are simply your private key and address printed on paper, literally a slip of paper you keep in a safe. For certain cryptocurrencies, especially Bitcoin, you can generate paper wallets offline using dedicated tools. They were popular in early crypto history but have largely fallen out of favor because they’re fragile (paper degrades, can be lost or destroyed), difficult to use for regular transactions, and expose your key whenever you need to import it into software to send funds. If you create a paper wallet, the moment you import that private key into any software to spend the funds, you’ve created a hot wallet attack surface. Paper wallets made sense in 2013; today, hardware wallets have made them obsolete for most users.
Custodial wallets are fundamentally different from the other three types. When you keep crypto on an exchange like Coinbase, Kraken, or Binance, you’re using a custodial wallet. The exchange holds the private keys; you only have an account balance in their internal database. This means you don’t need to worry about losing your seed phrase, the exchange is responsible for securing your keys. But it also means you don’t actually control your crypto in the meaningful sense. If the exchange gets hacked, freezes withdrawals, or goes bankrupt, you could lose access to your funds with limited recourse. During the FTX collapse in November 2022, millions of users learned this lesson devastatingly. They thought they owned crypto in their FTX accounts, only to discover they were general creditors in a bankruptcy proceeding with uncertain recovery prospects.
For most users, a reasonable approach is to use a software wallet for daily transactions and DeFi activity while keeping larger holdings in a hardware wallet. Custodial exchange wallets make sense only for actively traded funds that you’re comfortable losing in a worst-case scenario.
Seed Phrases: The Double-Edged Sword of Cryptocurrency
I want to highlight one more critical concept that separates crypto security from anything in traditional finance: the seed phrase and its profound implications.
When you create a non-custodial wallet, you’ll be presented with a sequence of 12 or 24 words. This is your seed phrase, the master backup of your wallet. With these words in the correct order, anyone can regenerate your private key and take complete control of your crypto. The seed phrase gives you absolute self-custody, but it also gives you absolute personal responsibility.
This is both the genius and the curse of cryptocurrency. Traditional finance gives you recourse when things go wrong, chargebacks, fraud protection, bank guarantees. Cryptocurrency gives you absolute control but zero safety nets. If someone steals your seed phrase, there’s no customer service number to call. Your crypto is gone.
Best practices for seed phrase storage are well-established but worth repeating: never store your seed phrase digitally (no photos, no cloud storage, no password managers unless encrypted). Write it on paper or stamp it into metal, companies like CryptoSteel or Billfodl make stainless steel storage devices designed to survive fires and floods. Store the backup in a physically separate location from your primary wallet device. Consider using a multisig setup for very large holdings, which requires multiple keys to authorize any transaction.
And here’s one piece of advice I rarely see emphasized: make sure someone you trust knows how to access your crypto in case something happens to you. Crypto inheritance is a genuine challenge. Millions of dollars in cryptocurrency have been lost because holders died without sharing their seed phrases with family members. This isn’t just theoretical. Chainalysis estimates that roughly 20% of all Bitcoin may be lost forever, much of it due to holders dying without passing on their keys.
Choosing the Right Wallet for Your Situation
Given everything we’ve covered, how should you actually choose a wallet? Let me cut through the noise with a practical framework.
For beginners holding under $1,000 in crypto: use the wallet provided by your exchange or a reputable software wallet like Trust Wallet or MetaMask. Focus on learning how transactions work and getting comfortable with the basic mechanics before investing in hardware wallets. The security risk of a hardware wallet you don’t understand properly far outweighs the security benefit over a software wallet you’re actually using correctly.
For intermediate users holding $1,000 to $50,000: consider a hardware wallet for your primary savings while keeping a software wallet for DeFi interactions and spending. Ledger devices are widely supported and relatively easy to set up. Keep your seed phrase properly backed up and test restoring from backup before depositing significant funds.
For serious holders with over $50,000: a hardware wallet is table stakes. Consider multisig solutions like Casa or unhosted.org that require multiple devices or people to authorize transactions. Your threat model expands at this level. You’re not just protecting against casual hackers but against targeted attacks. Professional-grade security might include air-gapped computers, dedicated devices for signing, and geographically distributed backups.
Regardless of your holdings, never keep all your crypto in one place. Spread it across multiple wallets. This isn’t just about avoiding eggs-in-one-basket risk. It’s about ensuring you maintain access to some funds even if one wallet fails or is compromised.
The Road Ahead: What Still Needs Solving
Crypto wallet technology has come remarkably far since Bitcoin’s earliest days, but significant challenges remain. The user experience of self-custody remains intimidating for non-technical users, and that friction is a major barrier to mainstream adoption. Seed phrases are fragile, confusing, and unforgiving.
Emerging solutions like social recovery, where trusted contacts can help you recover your wallet if you lose your keys, offer promising paths forward. Account abstraction on Ethereum enables smart contract wallets with features like multi-factor authentication, spending limits, and social recovery that could eventually make crypto as easy to secure as a traditional bank account. Companies like Argent and Soul Wallet are building these primitives right now.
But these advances come with their own trade-offs. Social recovery introduces new attack surfaces. What if your “trusted contacts” collude against you? Smart contract wallets have bugs that could result in lost funds. The tension between usability and security is a fundamental problem that the industry is still solving.
What I can say with certainty is this: the wallets you use today will look primitive in ten years. But the fundamental principle, that you are your own bank, with all the power and responsibility that implies, will almost certainly persist. Your private keys, your crypto. Lose them, and no one can help you. Understand this, internalize it, and build your security practices accordingly.